Dans le domaine de la cybersécurité, il y a toujours une nouvelle menace à l’horizon. La nouvelle astuce trouvée par des cyberpirates pour duper leurs victimes est de détourner les communications des institutions qui sont chargées de notre sécurité.
Serveur courriel piraté
Récemment, un serveur courriel appartenant au FBI (Federal Bureau of Investigation) a été piraté et utilisé pour envoyer des fausses alertes de cybersécurité à des milliers de personnes. L’incident a été divulgué publiquement par l’organisation internationale d’intelligence sur les cybermenaces, Spamhaus, le 13 novembre, 2021.
Plus tard, le FBI a confirmé l’incident dans un communiqué que vous pouvez trouver ici.
Spécifiquement, les pirates informatiques ont exploité le portail internet (LEEP) du service d’information de la justice criminelle du FBI pour obtenir accès et envoyer de fausses alertes. LEEP est une plateforme utilisée par les agences policières, les groupes de renseignements et les organisations policières. Les services offerts incluent des outils d’investigation, des ressources analytiques et des opportunités de réseautage professionnel au niveau des états et des municipalités.
Au lieu de simplement usurper une adresse courriel («spoofing ») semblable à celle du FBI, les cyberpirates avaient maintenant accès à une adresse courriel légitime du FBI, dans ce cas « [email protected][.]gov », qu’ils ont utilisée pour envoyer des fausses alertes intitulées « Urgent: Threat actor in systems. ».
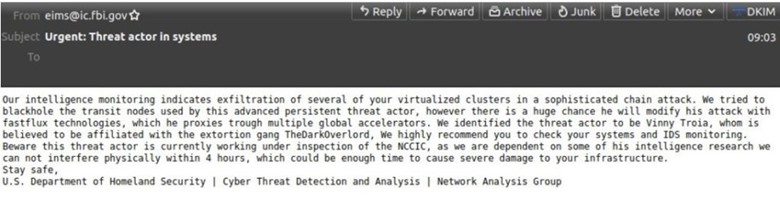
Capture d’écran de la fausse alerte reçue par Brian Krebs de Krebs on Security
Jusqu’à maintenant, il semblerait que l’objectif principal de l’attaque était d’accuser à tort Vinny Troia, un chercheur de sécurité et fondateur des firmes d’analyses du Dark Web Night Lion Security et Shadowbyte. Les courriels, aussi, affirmaient que Troia est activement affilié avec le gang de criminels dénommé TheDarkOverlord.
Cependant, dans les jours suivant, le criminel notoire pompompurin a revendiqué l’attaque. Dans une entrevue exclusive avec Brian Krebs, pompompurin prétendait avoir perpétré l’attaque dans le but d’exposer les lacunes flagrantes dans les systèmes de cybersécurité du FBI.
Apparemment, la vulnérabilité exploitée par le criminel n’était qu’une simple erreur de configuration de logiciel. Ensuite, il a exploité le system d’authentification à facteurs multiples pour intercepter le mot de passe initial utilisé pour enregistrer un nouveau compte directement d’après le code source HTML de la page web.
Au début, le piratage semblait n’être que le dernier d’une longue série de campagnes de diffamation lancée contre Troia en représailles pour sa divulgation d’informations sur le groupe criminel TheDarkOverlord. Selon Marcus Hutchins, un chercheur chez Kryptos Logic, le cybercriminel a tenté d’impliquer Troia dans plusieurs cyberattaques visant, notamment, ElasticSearch.
Pour une raison ou une autre, pompompurin a aussi pris l’habitude de s’acharner sur Troia en démontrant ses talents de piratage.
Un précédent dangereux est établi
Pour l’instant, il semblerait que le FBI ait évité le pire du danger puisque cette vulnérabilité n’a pas été exploitée par un auteur de cybermenace ayant un agenda plus sinistre. Cependant, cette histoire nous montre que personne, y compris le FBI, ne peut se permettre de devenir complaisant en matière de cybersécurité. Que ce soit aux États-Unis, à Toronto au Canada, ou n’importe où ailleurs dans le monde, toutes organisations doivent faire des tests d’intrusion (« penetration testing ») ainsi que des tests de vulnérabilités sur leurs infrastructures de façon périodique.
Quoi qu’il en soit, cet incident a établi un précédent dangereux. Si les cyberpirates peuvent utiliser des adresses courriel légitimes dans leurs tentatives d’hameçonnage, d’infection ou autres méthodes d’exploitation, la probabilité de leur succès augmente. On ne s’attendrait pas qu’une source d’information supposément hautement fiable et crédible, tel un serveur de courriel du FBI, puisse être compromise si aisément. La formation continue en cybersécurité des employés peuvent aussi aider les entreprises à détecter et prévenir les cyberattaques comme le hameçonnage («phishing ») et l’ingénierie sociale (« social engineering »). Il faut garder les yeux bien ouverts et rester vigilant!